Resources
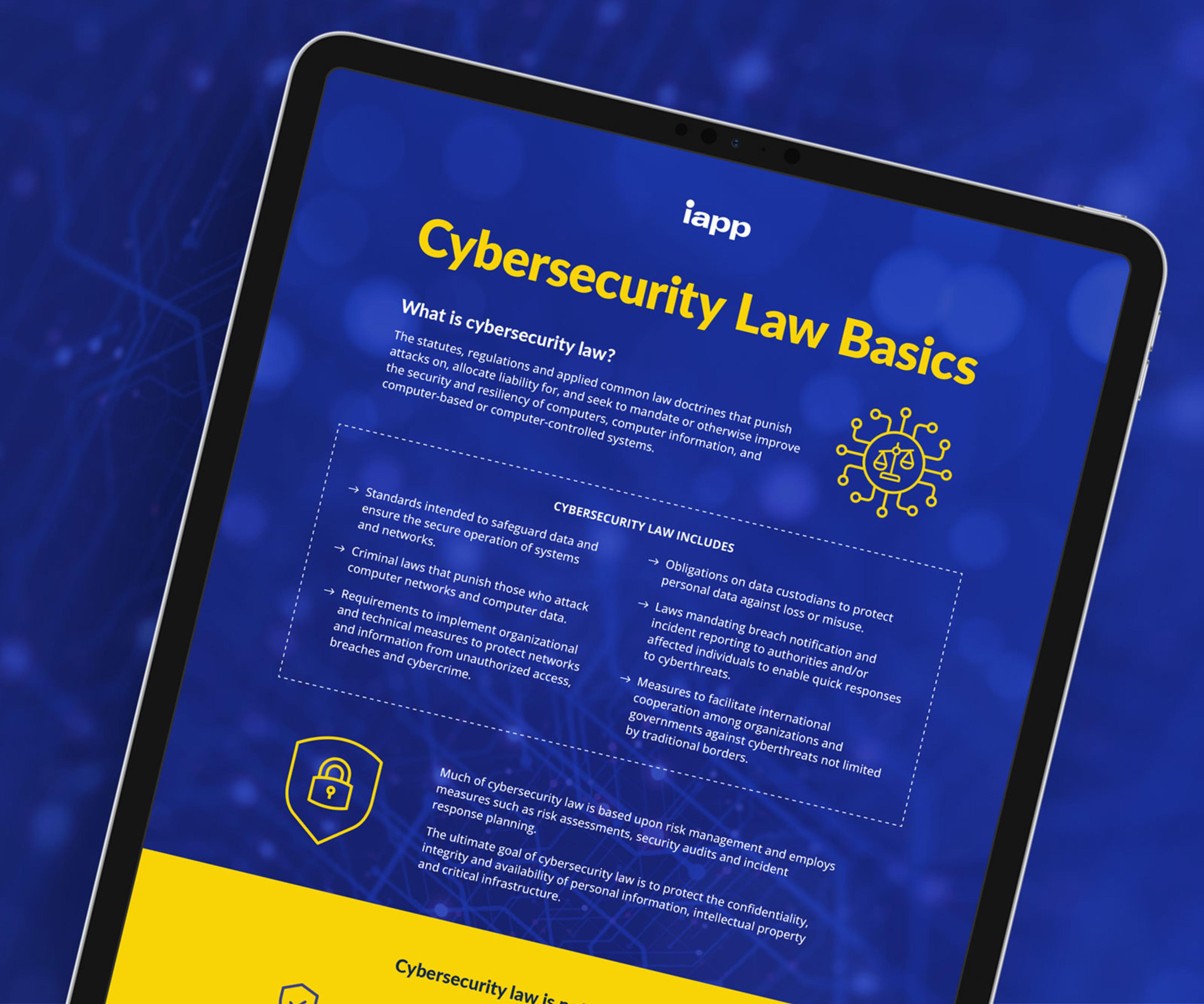
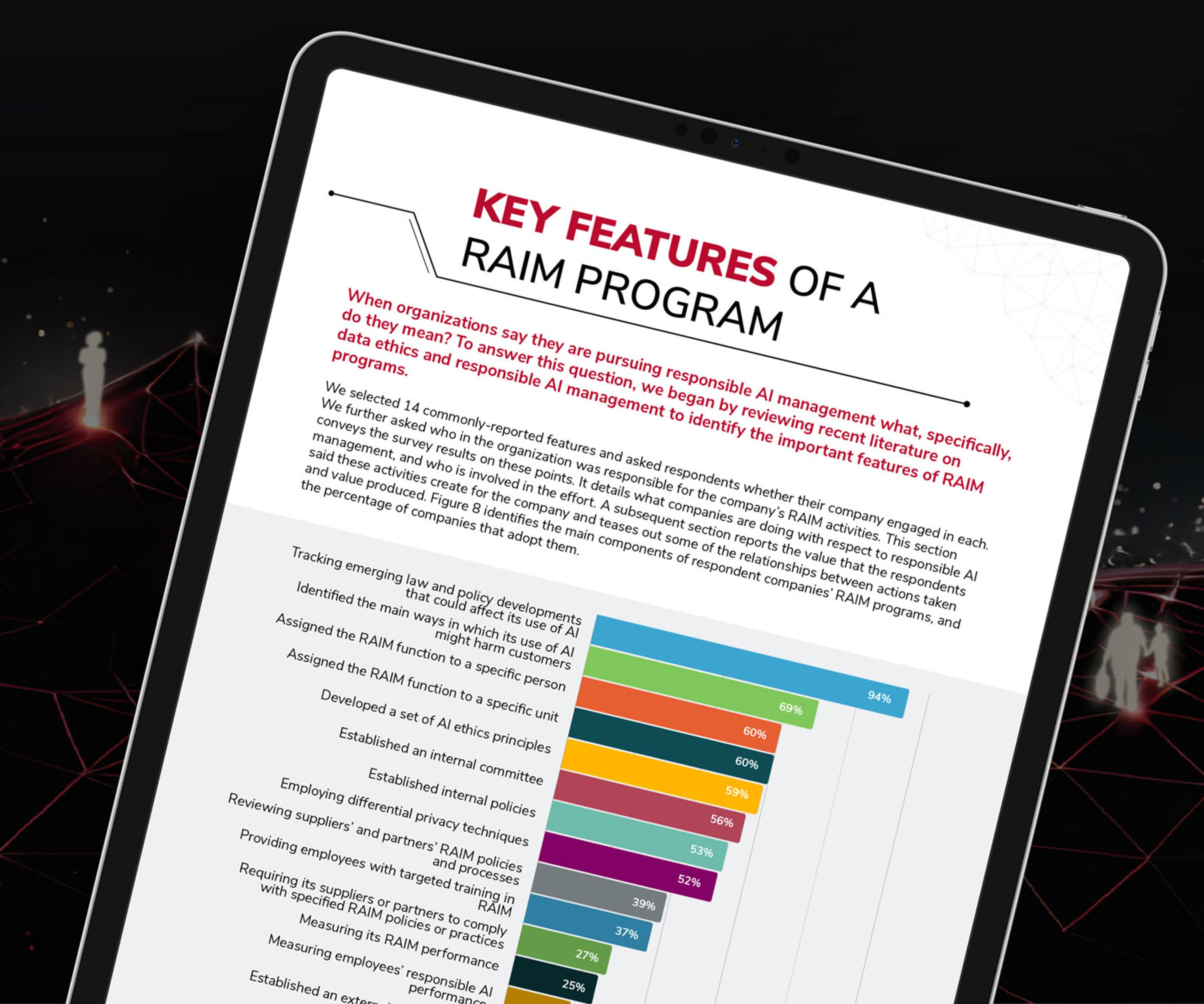
Developed by industry experts and thought leaders, IAPP resources provide the tools and information you need for your organization's AI governance, cybersecurity law and privacy programs.

New and featured resources
US State Privacy Legislation Tracker
TOOLS AND TRACKERSMEMBER
GDPR at 10: A Look Back at the Past 10 Years
INFOGRAPHIC

Member-exclusive resources
See all reports
Organizational Digital Governance Report 2025
REPORTMEMBER

EU Digital Laws Report 2025
REPORTMEMBER

Privacy and Consumer Trust Report
REPORTMEMBER

Access member-exclusive resources
Top subjects
See all subjects
Global AI Law and Policy Tracker
TOOLS AND TRACKERSMEMBER
Global AI Governance Law and Policy 2025: Jurisdiction Overviews
RESOURCE ARTICLEMEMBER

EU AI Act Regulatory Directory
TOOLS AND TRACKERSMEMBER

US State Privacy Legislation Tracker
TOOLS AND TRACKERSMEMBER
US State Comprehensive Privacy Laws Report 2025
REPORTMEMBER
US State AI Governance Legislation Tracker
TOOLS AND TRACKERSMEMBER
California Privacy and AI Legislation Tracker
TOOLS AND TRACKERSMEMBER
Head-start tools and templates
View all head-start tools and templates
Transfer Impact Assessment Templates
TOOLS AND TRACKERSMEMBER
EU Standard Contractual Clauses
TOOLS AND TRACKERSMEMBER
Expedited Vendor Privacy and Security Assessment Checklist
TOOLS AND TRACKERSMEMBER
Consumer Privacy Notice Template
TOOLS AND TRACKERSMEMBER
Data Security Program Cheat Sheet
INFOGRAPHIC

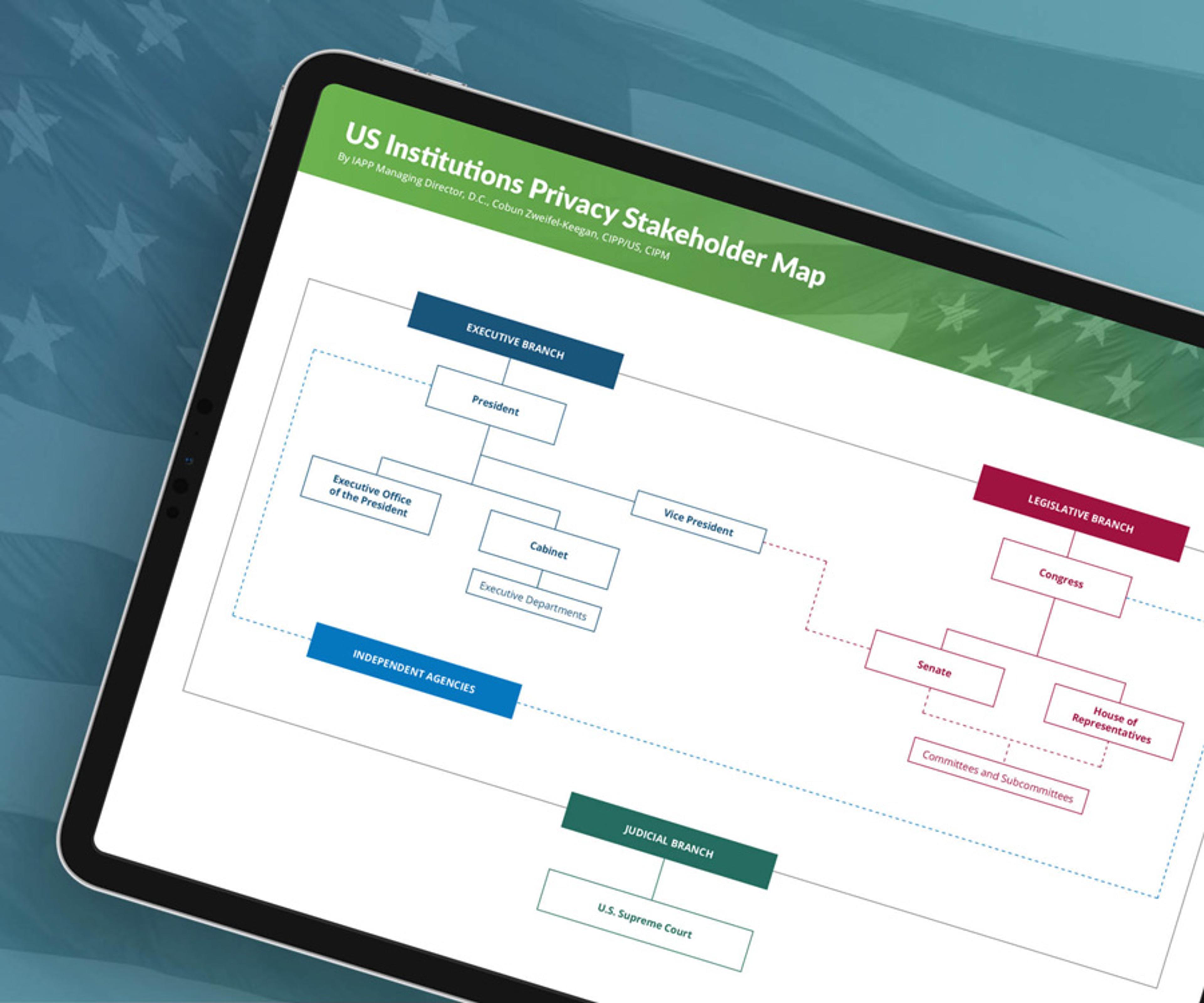
US Institutions Privacy Stakeholder Map
TOOLS AND TRACKERSMEMBER
European Institutions and Regulators Digital Governance Stakeholder Map
TOOLS AND TRACKERSMEMBER

Sample DPO Service Agreement
TOOLS AND TRACKERSMEMBER
Sample CCPA Privacy Notices
TOOLS AND TRACKERSMEMBER
Sample Data Processing Agreement
TOOLS AND TRACKERSMEMBER
DPO Job Description
TOOLS AND TRACKERSMEMBER
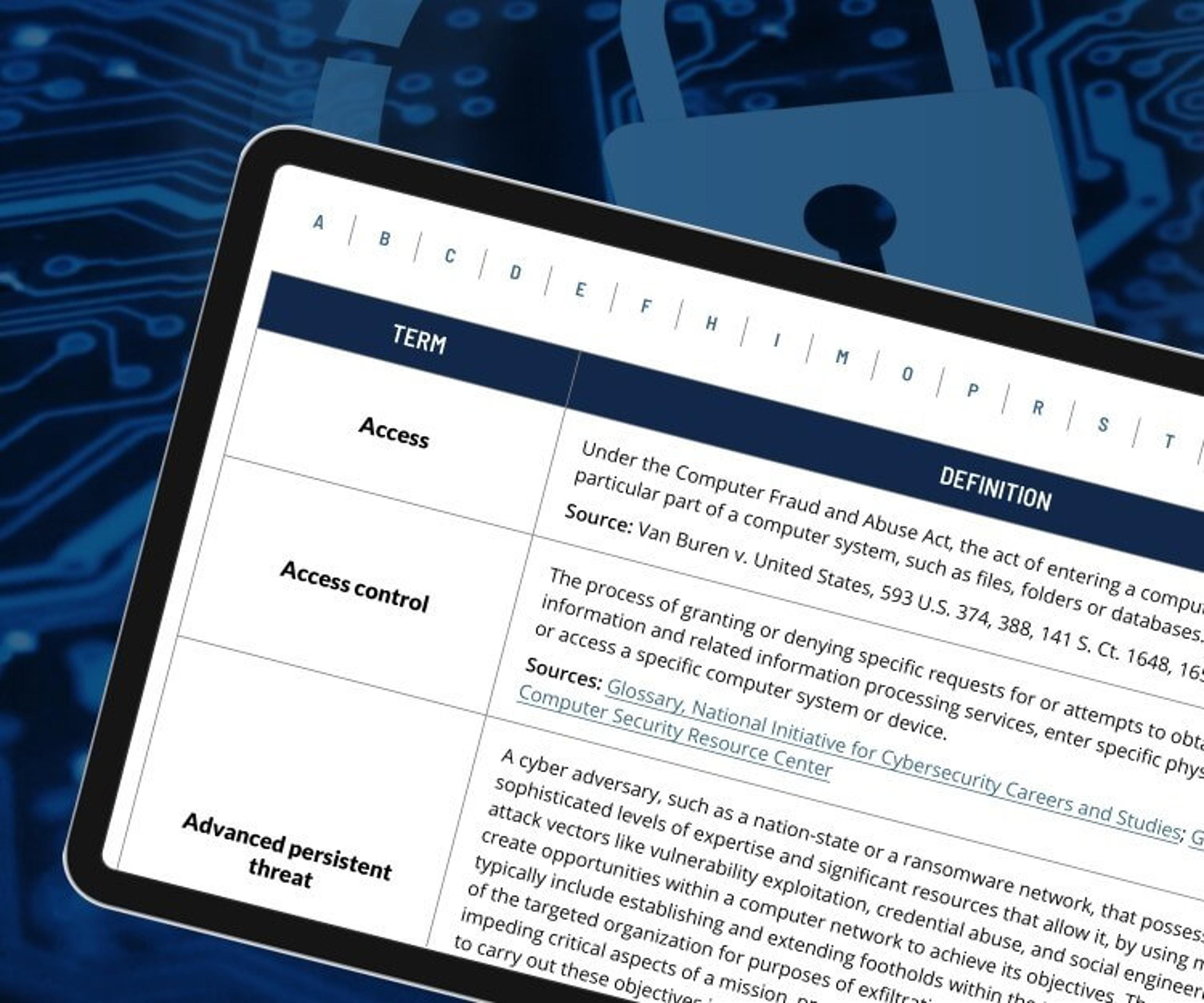
Search our library of 750+ resources
Search, filter and find the content you need — fast.
Interactive content
Web conferences, tools and trackers and other resources to take your digital responsibility program to the next level.
Live web conferences
Updates on industry trends and insights from thought leaders — right from the comfort of your own desk.
Tools and trackers
Keep up with rapid developments in digital responsibility with legislative trackers, enforcement tools and more.