While many are now focused on the newly minted privacy enforcers in the U.S., such as the Consumer Financial Protection Bureau and the Federal Communications Commission, the Federal Trade Commission was never the only privacy enforcer in the United States. The Office for Civil Rights, a part of the Department of Health and Human Services, has been on the privacy beat as well for a number of years. While its resolutions do not broadly apply to every company, since HIPAA only applies to “Covered Entities” and “Business Associates," as more companies enter the health care space, HIPAA is more of a consideration for many companies. Moreover, even if HIPAA is not applicable to your company, there are some issues, as well as best practices, that can be identified from an examination of OCR’s enforcement patterns.
There are six key points that companies should be aware of that can be drawn from public enforcement patterns.
Two terms that are important to understand in HIPAA enforcement are Resolution Agreements and Corrective Action Plans (CAPs). These two terms are part of process for managing and handling complaints, and this process is more fully explained on OCR’s website. In general, the possible outcomes of an OCR investigation are threefold: a finding of no violation; OCR obtains voluntary compliance, corrective action, or other agreement, or OCR issues a formal finding of violation. It is the latter category, at least as expressed by public Resolution Agreements, that provides interesting data points for companies to consider.
OCR self-identifies 30 Resolution Agreements that it has obtained, including two Resolution Agreements that were announced in a joint way. There are other CAPs and outcomes that are referenced on the OCR website in a more general way, but the Resolution Agreements allow a review of certain trends regarding OCR enforcement in those 30 cases.
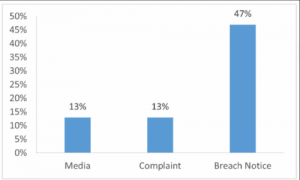
First, examining how these cases occur is important. In 73 percent of the cases, the source was clear. In 13 percent of the cases, the source appears to be the result of media report; 13 percent was the result of complaints; 47 percent was the result of breach notification from the CE or BA, and in 27 percent, the source was unclear.
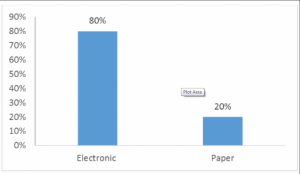
Second, it is also interesting to note the types of data that lead to enforcement: 80 percent of the cases involved electronic data, while 20 percent were paper cases.
Electronic v. paper
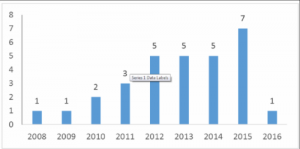
Third, the number of cases per year is important because enforcement is trending. The chart below shows this trend. While 2016 has only one case so far, it is likely that this number will increase to be more consistent with 2014 and 2015 given past experience.
Cases by year
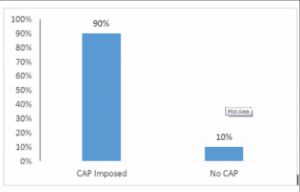
Fourth, it should be noted that of the 30 Resolution Agreements, 90 percent of them had a CAP, and the one that did not presented some unique circumstances.
However, not all CAPs are created equally. A fifth point to consider is that there appears to be a relatively “standard” CAP, similar to what the FTC had been doing in the data security realm with its “boilerplate,” but previous specific requirements with OCR were not as “standard” as with the FTC. If one examines the CAPs subjectively and tries to categorize them, the standard CAP was used in just less than 50 percent of the cases, a CAP with additional risk assessment requirements was used in about 22 percent of the cases, and in just under 30 percent of the cases, either no CAP or a CAP with lesser requirements than normal was the basis for relief.
The sixth point, turning to other remedial issues, while OCR typically seeks a three-year CAP, the average length of the CAPs that were entered was two years. Also, it should be noted that the average monetary relief obtained by OCR was just under $1.1 million in these cases.
Now that privacy and security issues are front and center for many companies, OCR’s enforcement pattern is important to note and understand, since a public Resolution Agreement can result in a compliance program of two years or more and an average fine of more than $1 million.