Blockchain 101: An introduction


Contributors:
Jedidiah Bracy
Editorial Director
IAPP
First, it was "cloud computing," then "big data," followed by the "internet of things" and "artificial intelligence." Buzzwords from technological paradigm shifts that eventually push the privacy management envelope. So here we are in 2018, and the word most flashed in news reports and blog posts seems to be "blockchain."
Yes, blockchain may be the future of secure banking. It may save companies tens of millions of dollars managing their supply chains or revolutionize identity access management. It may help feed the homeless in large cities. Heck, it might help me walk my dog in the morning.
OK, the last one is obviously untrue, but the "Blockchain Notion" seems to be everywhere and in every solution, but what is it?
No, it's not bitcoin. And no, it's not the silver-bullet solution that many people think it will be. That said, some of the world's biggest and most influential companies — not to mention, government regulators — are taking the promise of blockchain technology very seriously, and it will likely affect the jobs of privacy practitioners. At the very least, it's a concept that privacy pros should have a basic understanding of.
Here's one ... explanation:
True, that wasn't a serious take, but, over the course of the next few weeks, Privacy Tech will feature several posts diving into blockchain. The field is developing rapidly, so this won't be "The Authoritative Explanation of Blockchain," but hopefully it will help you familiarize yourself with this burgeoning concept, as well as some of its basic definitions and related policy issues.
At its most basic definition, blockchain is a decentralized ledger of transactions over a period of time that is protected and linked together by cryptography. The concept was invented by an unknown individual (or group, who knows?) named Satoshi Nakamoto in response to the global financial meltdown in 2008. It's helpful to understand the inspiration behind the concept: The "too-big-to-fail" banking system involved trusted, centralized authorities — once one went down, the whole system was at risk. Blockchain avoids that single point of failure through a trustless, decentralized network. Of course, there are caveats, but we'll save that for later.
In 2008, Nakamoto introduced the world to bitcoin. First as a blog post, then as a publicly available cryptocurrency, bitcoin was the first non-central framework to solve the "double-spend" problem. Before the bitcoin solution, when using digital cash, adversaries, in theory, could counterfeit digital currency by copying the files and spending them at will. Trusted banking authorities can track digital spending, but, as was already mentioned, they're also single points of failure. Instead of trusted authorities, this system relies upon cryptography. It's essentially a "trustless," peer-to-peer network.
If you want to go deeper into the history of finance, the double-spend problem, and how bitcoin works, I recommend checking out this video put out by the Center for Democracy & Technology.
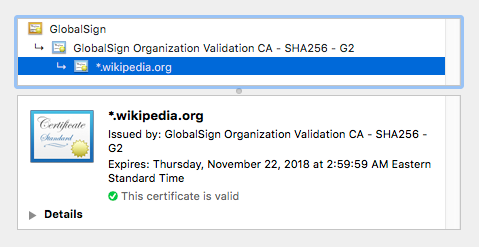
The bitcoin concept, in opposition to centralized banking, uses an agreed-upon cryptographic protocol, in part called proof-of-work, to ensure that changing the transactions in the bitcoin ledger would be computationally infeasible. The bitcoin protocol uses a one-way cryptographic hash function called SHA-256. Users of PGP email, or anyone familiar with the HTTPS protocol, will have seen SHA-256 at work.
OK, we're getting into the weeds a little bit here, so let's step back for a second and think about how bitcoin relies upon the blockchain.
Each block contains a list of transactions: Bob pays Julie 100 units; Julie pays Alice 75 units, and so on. Each block also represents a snapshot of time. In the bitcoin protocol, a new block is created about every 10 minutes (there are other cryptocurrencies that have more frequent timestamps). To ensure the ledger of transactions in the block is immutable, "miners" use computing power to solve the cryptographic hash functions attached to a block. Miners have an incentive to find the "hash digest" because, once it's found, the miner credited with the solution is awarded a certain amount of bitcoin. In addition to the miners, "nodes" broadcast and continuously update the blocks. The more nodes in the network, the more secure it becomes. The proliferation of nodes is how the blockchain is decentralized.
Though hash functions are difficult to solve, they're easy to verify. This is where the trustless incentive is built into the system. In other words, I don't need to "trust" other users on the network. Instead, the cryptography ensures the blocks are protected, and if anything in a previous block is altered, everything that comes after the alteration would be noticeable because it's based on a one-way hash function: The input always affects the output, so any changes made would catalyze a domino effect of changes throughout the chain.
Once the hash function has been solved for that block, it is announced to the network of nodes. The nodes on the network get a copy of the latest block in the chain and the same cycle happens continuously for each block. The miners are competing against one another to solve the cryptographic hash function so they get paid more bitcoin. To connect the chain, each block contains the hash function of the previous block. The longer the chain gets, the more secure it becomes.
If you want to learn more about the math involved, the video below does an excellent job describing and animating the process. It also helps bring understanding to public-private key encryption.
The miners solving the difficult math problems use advanced computing power because they essentially have a one-in-a-billion shot of correctly guessing the number. Computing power takes energy, and that's why you've likely read stories about how a year of bitcoin uses the same amount of electricity that supplies all of Denmark over the same amount of time.
As a related information security issue, "cryptojacking" has become a thing in the digital world, where miners essentially outsource their needed computing power to other individuals' browsers, computers and devices. They are basically running programs to solve the super hard math problems in the background of other people's computers. In addition to draining your battery and running up your electricity bill, this introduces a new vulnerability to your computer.
Bitcoin is but one of countless cryptocurrencies in existence. Ethereum is another common currency that uses a different protocol. But cryptocurrencies are public and involve digital currency. That's not necessarily the main area that big companies are looking to use the blockchain.
In the next post, we'll discuss the emergence of "permissioned blockchains," "smart contracts," and other non-cryptocurrency uses of blockchain.
Top image is a screen shot from 3Blue1Brown'svideo on cryptocurrency.
Contributors:
Jedidiah Bracy
Editorial Director
IAPP



