Industry of Privacy Project: Early Insights


Published
Contributors:
Andrew Clearwater
AIGP, CIPP/E, CIPP/US, CIPM, FIP
Partner, Privacy and Cybersecurity
Dentons
Dennis Holmes
Privacy Policy Manager
Introduction
As the field of privacy has developed, solutions to privacy concerns have multiplied in the marketplace. Tech vendors, service providers, consultants, law firms—all have broadened and deepened the offerings they have for privacy professionals to purchase in governing data, and data is becoming a company’s most valuable asset. Privacy is a dynamic industry that has moved quickly, so quickly that few have stopped to take stock in how far the industry has come, and perhaps more importantly, what the industry has become. The IAPP Industry of Privacy Study seeks to do just that. This study is a comprehensive survey that will cover the entire industry of privacy and inventory all of the solutions and services available; and categorize those solutions and services into meaningful segments that are useful to privacy professionals. This project will allow privacy pros to better understand their organizational maturity and risk profile. Further, it will provide IAPP members with tools to engage a broader audience of influencers who are making spending decisions on privacy-related solutions and services within the enterprise. The industry of privacy deserves to be documented and understood in its entirety. This is still a work in progress but we would like to share some of our early insights to give you a taste of what’s to come.
Contents
Groundsetting
- The Need for Privacy Skills Has Never Been Higher
- The Rewards for Privacy Skills Continue to Grow
Preliminary Quantitative Survey Results
- Myth: Small Companies Do Not Spend Money on Privacy-Related Products or Services
- Myth: The IT Department Controls the Spending on Privacy-Enhancing Technologies
Qualitative Data From Discussions
- Privacy and Security: Better Together
- Finding Support
- Influence Can Be More Important Than Budget
Focus on Data Breach
- The Influence of Privacy Professionals
Conclusion
Groundsetting
The Need for Privacy Skills Has Never Been Higher
The industry of privacy has come of age. Retailers are linking loyalty card data with social media information to predict purchasing patterns; smart phones track our location and how fast we are moving, and websites record our clicks, what we buy and if we share or like something. Today we are collecting and aggregating more information as a society than ever before; as much as 2.5 quintillion bytes of data are generated each day. Or put another way, 90 percent of the data in the world today has been created in the last two years alone.McKinsey & Company, Inc., an American global management consulting firm, projects that the United States will need 140,000 to 190,000 more workers with “deep analytical” expertise and 1.5 million more data-literate managers. Peter Sondergaard, senior vice president at Gartner and global head of research, estimates that by 2015 the U.S. will need 1.9 million more data scientists, because data analytics is one of the fastest growing fields in IT. He further predicted that every Big Data-related role will create employment for three people outside of IT. Further, accounting and auditing firms have enjoyed the windfall of the privacy compliance auditing required to review and manage these complicated systems.
For data, there are rules that must be followed. In the United States, federal and state laws and regulations protect the privacy of personal information and more are on the way. Violations of some these laws carry a hefty price tag in the form of sanctions, while other means of enforcement such as consent decrees with the Federal Trade Commission can be more burdensome than costly.
Though the Federal Trade Commission has been, and continues to be, very proactive about holding companies accountable for their privacy promises and data collection and use practices, it is not the only federal agency paying attention to privacy in the private sector. Recently, the Security Exchange Commission issued guidance on cybersecurity and now requires companies to clearly detail their risk of a cyber-attack. Additionally, in today’s global economy, data transfers are almost never exclusively intra-national. The European Union has a swath of data protection regulations by which companies processing the personal information of EU citizens are expected to abide, regardless of where the company is based. At this intersection of risk and complexity there is demand for skilled privacy professionals and those privacy professionals are being given larger budgets with which to protect their organizations’ valuable assets.
The Rewards for Privacy Skills Continue To Grow
The privacy boom has positive compensation implications for privacy professionals. Practical privacy knowledge allows professionals to increase both their value to the company and its bottom line. The 2012 IAPP Privacy Professionals Role, Function and Salary Survey revealed that respondents working for U.S.-headquartered firms earned an average of $123,030, followed by firms based in Europe at $114,116 and Asia-Pacific organizations at $113,527. Professionals with privacy certification like CIPP/US reported a median salary $13,000 higher than their contemporaries with no such distinction. But privacy professionals need tools with which to perform the increasingly important jobs with which they’ve been tasked. There are myriad opportunities in the privacy industry for technology vendors, service providers, law firms, consultants and other firms to develop products and services that offer solutions to the privacy concerns that abound in the marketplace.
Preliminary Quantitative Survey Results
The initial Industry of Privacy survey generated some interesting results. A more complete report will be forthcoming, but there are a few initial results worth sharing. The survey saw responses from 413 privacy professionals around the world, with just 23 percent of them working for firms that solely did business in the United States. More than half, 50.98 percent of respondents, identified themselves as working at private-sector firms with in-house positions. Across all spending categories, these privacy professionals working in the private sector, in-house reported more decision-making power and influence on privacy budget than any other position in the privacy landscape. 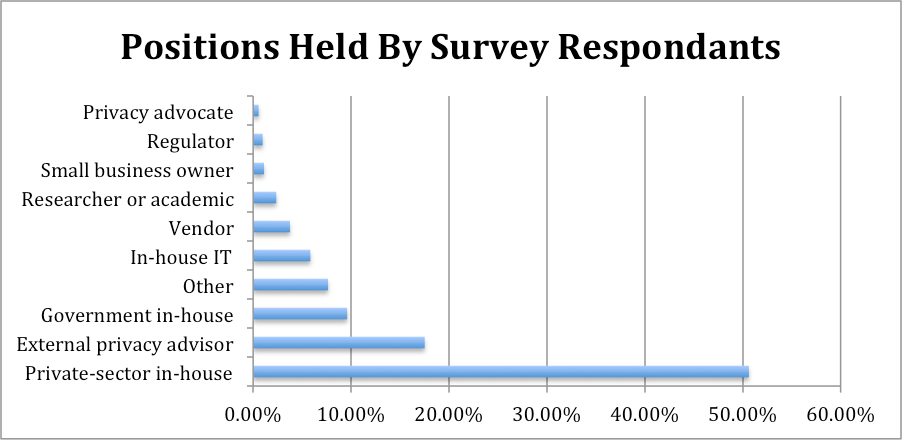
- Assessments & Audits
- Staff Augmentation (Experts on Demand)
- Process Integration (Getting People To Work Together)
- System Integration (Getting Technology To Work Well Together)
- Other Type of Consulting Service
- Backup and recovery software,
- Data loss prevention,
- eDiscovery software,
- Governance & compliance solutions,
- Identity and access management and
- Mobile device management.
Myth: Small companies Do Not Spend Money on Privacy-Related Products or Services
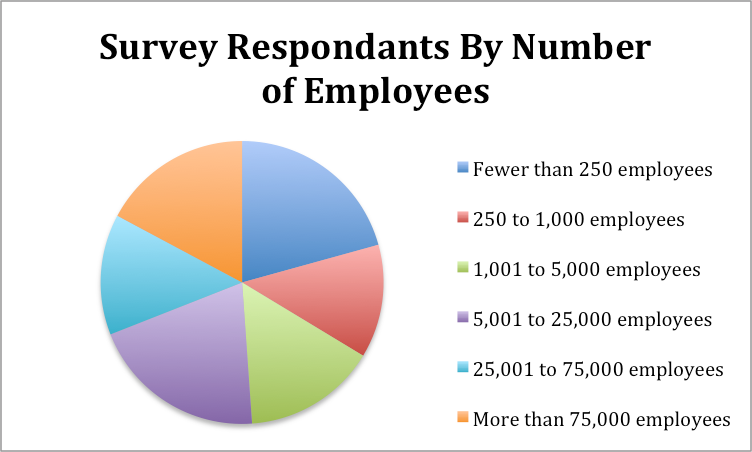
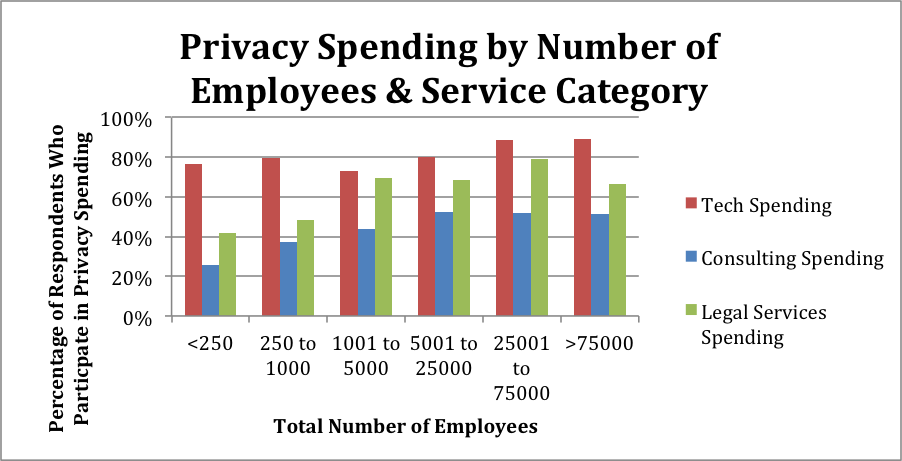
The belief that small companies are not willing to spend their precious, and likely limited, capital on privacy compliance is understandable. Our findings, however, do not support that belief. Survey results reveal that company size may have little to do with spending on privacy. In conducting our survey, we determined the size of an organization by asking our respondents to select their total number of employees from six numerical ranges. 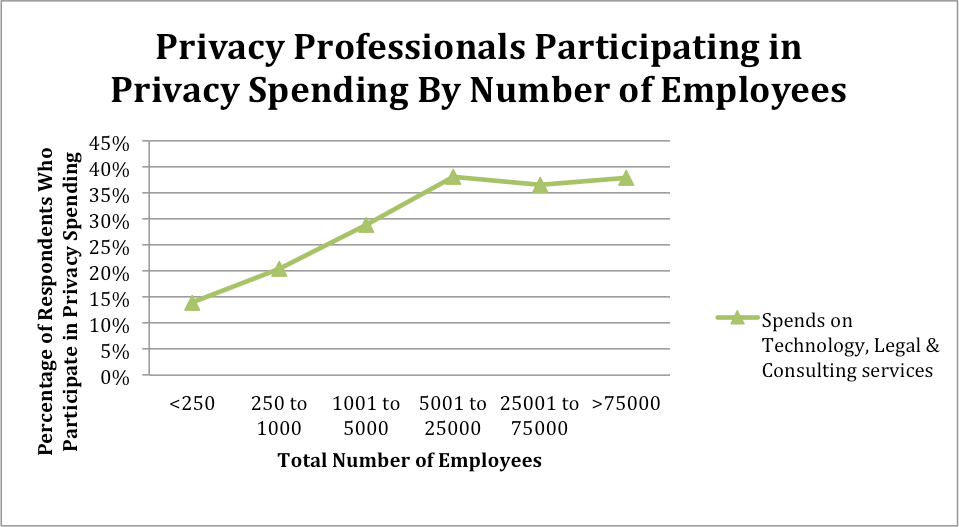
Professionals in large companies are more often in control of privacy spending but it’s not by the margins that were expected. For example, for companies with 250-1000 employees, 20 percent of the privacy professionals were investing in external privacy resources. At the other end of the spectrum, for companies with greater than 75,000 employees, 38 percent of the privacy professionals were investing in external privacy resources. Obviously the amount that is spent by a company with a larger budget is greater but influence over privacy spending is not solely the domain of privacy professionals in medium- and large-size organizations.
We also found that the percentage of companies that reported spending specifically on privacy-related technologies only varied, on average, 5 percent across all size ranges. Small companies reported spending on technology service at nearly the same rate as large companies. This demonstrates that there is no meaningful difference related to organizational size with regard to spending on technology products and services; it is a priority across the board.
Myth: The IT Department Controls the Spending on Privacy-Enhancing Technologies.
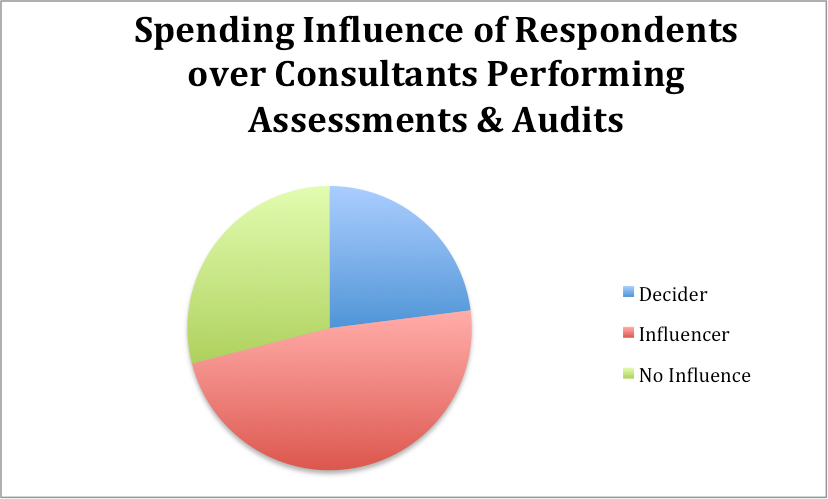
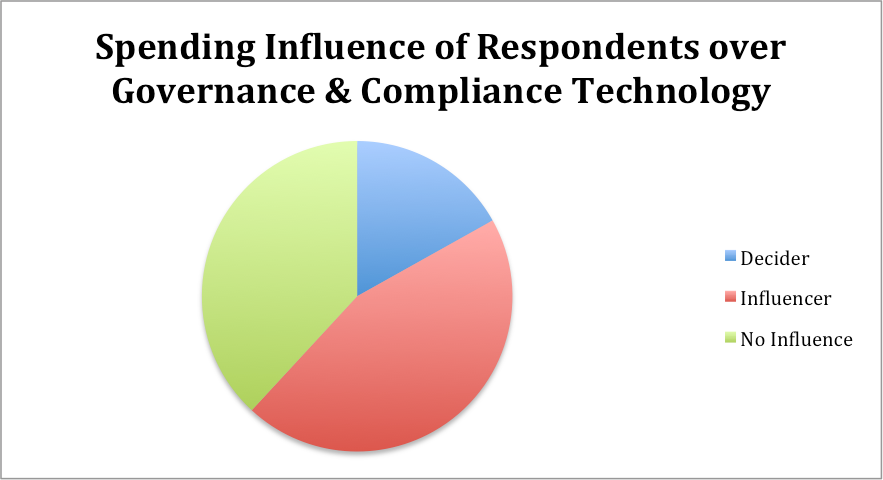
Organizational structure varies widely from company to company. Privacy departments, however, generally fit into that structure in one of two ways. Either the IT department handles privacy matters or there is separate team, typically housed in the legal or “compliance” departments. In the latter scenario, it is a common belief that members of the privacy team are not involved in decisions about purchasing privacy-related technology products or services. Our findings suggest that privacy professionals outside of IT are, indeed, purchasing privacy-enhancing technologies.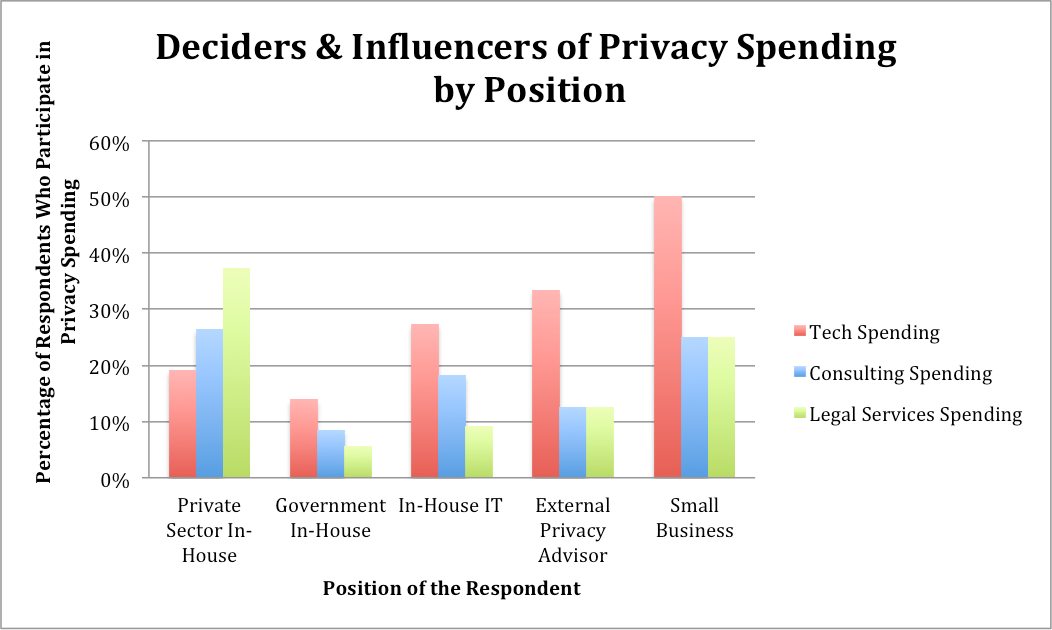
We found that 27% of the IT professionals surveyed reported having influence or decision-making power over spending on privacy enhancing technologies compared to 19% of private-sector in-house privacy professionals. The 8% difference between IT and private in-house professionals that have some influence spending on privacy-related technology reveals that the gap in influence over technology spending is less than many would expect.
We also found that the percentage of IT and private-sector in-house professionals who reported having influence over spending on privacy technologies shifted based on the type of technology product being purchased. With mobile device management technology, IT professionals reported having 60% influence and 20% decision-making power. A full 80% have some say. While 43% of private-sector in-house professionals reported having influence, and 3% reported having decision-making power. For data loss prevention products, the story is slightly different because while the same 3% of private-sector in-house professionals reported having decision-making power and 47% reported having influence, only 60% of IT professionals reported having input in that area. This suggests spending on privacy-related technology products depends on the technology product.
Even without a budget or final decision-making power, privacy professionals outside of the IT department still have a substantial amount of influence on spending with regard to privacy technologies. These findings also suggest that organizational privacy leaders do not perform their work in isolation and collaborate with other internal leaders to achieve their privacy goals.
Qualitative Data From Discussions
The statistics that have been collected as part of our research have also been supplemented by many conversations with industry experts to better understand privacy on the ground. A common theme that developed in these conversations was the collaborative nature of privacy within organizations. Part of this stems from the wide variety of organizational structures. The Privacy Professionals Role, Function and Salary Survey conducted by the IAPP in 2012 revealed that the majority of the privacy roles reside in legal or compliance but there are many other organizational structures.
Reporting Structure of Corporate and Government Privacy Offices
| Department | 2012 |
|---|---|
| Legal | 30% |
| Compliance | 29% |
| Information Security | 9% |
| It is its own function reporting directly to the top executive | 9% |
| Risk Management | 5% |
| Information Technology | 5% |
| Operations | 3% |
| Ethics and Corporate Responsibility | 2% |
| Business Unit | 2% |
| Audit & Quality Assurance | 2% |
| Marketing | 1% |
| Human Resources | 1% |
(Source: IAPP 2012 Privacy Professionals Role, Function and Salary Survey)
Privacy and Security: Better Together
At a minimum, the field of privacy involves two groups of professionals working together: privacy and security. Privacy professionals do not need to be technical but they need to know the IT folks and they need to know them well. The degree of openness between these roles can generate a lot of privacy progress within an organization. Mike Money, Director in Protiviti’s Technology Risk Services Practice, put it this way:“If security and privacy work together, you have two budgets. You are defending the same information.”
There are parallels between the privacy and security field. In either field you are trying to convince management to prevent bad things from happening, but it’s always hard to pitch return on investment when that bad thing hasn't happened. Learning to craft a compelling narrative of risk reduction is an essential skill in this setting and it’s an area where cooperation can lead to greater success. Oftentimes, security professionals are the origin of privacy projects. Discussions with many professionals in the field revealed that external privacy resources were often contacted when security professionals raised an issue which was passed to legal, then shared with privacy, who then got in contact with their trusted vendors and advisors. 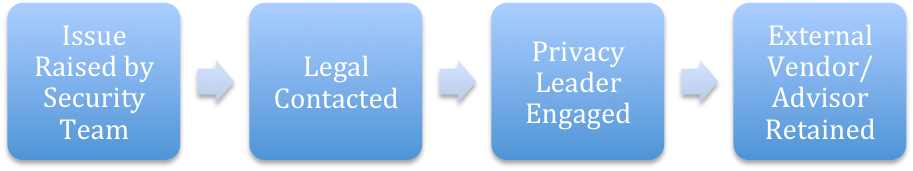
Another reason privacy professionals should pay attention to security is because security can teach the field of privacy how to gain power, budget and decision-making authority. Chris Babel, CEO at TRUSTe, is familiar with the parallels between these fields, and said:
"Privacy is like security 15 years ago - unclear privacy leadership in the company with no CPO just like CISOs didn't exist 15 years ago; most privacy services are people and/or consulting based and in need of technology to scale to meet enterprise needs; privacy is not designed into products from the beginning or thought about in product management and engineering; and privacy professionals lack a dedicated budget which requires efforts to solicit one in other parts of the organization."
The analogy isn’t perfect, but in the mid-’90s the CSO was a fairly new position with influence but oftentimes no budget. Fast-forward to today and the CSO is a key decision maker and trusted advisor with control over their own budget. Many feel the CPO will follow suit.
Finding Support
The goal of many privacy professionals is to make privacy a constant value, rather than a pendulum of complacency and panic. Sometimes the ability to accomplish this goal comes down to the structure of privacy within your organization. John Kropf, who has held privacy leadership positions both in the private sector and in government said:Privacy is a concept that doesn't lend itself to a bumper sticker definition.
Overcoming this identity crisis requires broad training and leveraging of relationships in leadership positions. Getting buy-in at the general counsel level can allow you to champion a cause in a way that allows for better organizational support. Every privacy professional is looking for ways that they can better influence the organization and part of that quest involves garnering better control or influence over the privacy budget.
Kirk Nahra, Partner with Wiley Rein in Washington, DC has the following advice:
"You need to be aware of two things: 1) You need to be aware of what your company does. 2) You need to pay attention to the problems hitting everybody else."
You need to know what data you have and what you do with it. Once you have that covered, look to the challenges faced by other companies. Even if those challenges have not materialized as an issue for you, looking to other people can tell you more about the risks you face and they can help you make your case for spending on privacy. It's always better to have an example. When you can say, “this is a real risk, look at what happened to x,” you can make an intangible risk much more real. Paying attention to the external environment is extremely important in gaining budget influence.
Influence Can Be More Important Than Budget
Very often the privacy professional is a gatekeeper, and influencer, and they may bring vendors and service providers to the table, but they are not the person with the budget. Simon McDougall, leader of Promontory’s global privacy and data protection practice, advises firms on governance, risk, and regulatory issues related to their data and records. He has found that for the majority of his work:"The CPO is often a stakeholder rather than a budget holder."
Because this is often the case, strength and the ability to influence others becomes an essential trait for success. A CPO with a strong ability to influence privacy spending will be able to take proactive measures and hire the necessary vendors and advisors to carry out risk assessments and benchmarking. Without influence, CPOs are left to wait for near misses or incidents that increase the value of privacy, if only momentarily, to deal with the risk. These sorts of post-incident engagements can be costly. A great way to increase influence is to increase privacy training within your organization. More understanding will likely lead to greater influence, better risk management, and lower long-term costs for you organization. Need budget for that? While we don’t yet have hard numbers, the anecdotal evidence we collected suggests that while consultants are engaged by companies quite often for small projects, their big money is made on incident response. In essence, money spent on prevention is much smaller than the money spent on repairing damage.
Focus on Data Breach
Businesses must work with a large collection of vendors from a variety of disciplines to reach their privacy goals. At least five major categories of products and services serve the needs of companies seeking to improve breach preparedness with risk assessments, mitigation and compliance or post-breach analysis, notification/reporting, and monitoring and recovery. These categories are:- Consulting Services: Businesses frequently rely on the experience, resources and tools that consultants offer to assist with risk assessment, compliance and data breach preparedness or response.
- Information Technology: Data breach prevention, analysis and response can be enhanced by information technologies.
- Consumer Services: Notification, call center and identity protection products seek to help companies maintain trust while meeting complex obligations.
- Cyber Liability Insurance: Insurance can protect companies in case of a cyber attack with liability associated with the loss of customer or employee data.
- Legal Services: Law firms offer a wide variety of privacy services ranging from risk mitigating services such as planning and implementing privacy and security programs to responsive services such as assistance with regulatory response, investigations, remediation and litigation.
The Influence of Privacy Professionals
Organizational approaches to privacy differ drastically and there exist many factors that influence an organization’s privacy strategy such as size, industry and demographic. Regardless, responsibility for an organization’s privacy is sometimes levied on a security team within the enterprise rather than a dedicated privacy professional. While designating privacy responsibility to a company’s security team is partly a product of the organization’s posture, another explanation can be found in the misunderstanding of the concept of privacy. The terms security and privacy are often conflated, when, in actuality, the terms represent independent, yet related, concepts. Privacy is a much more encompassing term, of which security is simply one important aspect. For companies to fully understand the increasingly complex issues of privacy that are emerging in today’s world it is imperative that they understand the difference between the terms. In its 2013 data security and privacy report, Forrester Research recognized that “privacy does not begin and end with security . . . Ensuring privacy requires a union of technology, policy, and culture, and a harmony between many business units from security to legal to HR to employees.”
As costly data breaches grow in number, frequency and complexity, dedicated privacy professionals become not only a luxury for large resource-rich companies, but an important and profitable investment for all organizations. Forrester Research uncovered the top factors that influence the cost of a data breach and further concluded that one of the most profitable investments companies can make is the appointment of a professional with enterprise-wide responsibility. PWC’s 2014 global information security survey echoes the increasing importance of privacy professionals:
Today, adversaries are constantly sharpening and evolving their capabilities to exploit new vulnerabilities. Addressing these threats will require that organizations approach activities and investments with best-available knowledge about information assets, ecosystem threats, and vulnerabilities…. [The most successful security programs] are aligning security with business needs, setting standards for external partners, and, in general, rethinking the fundamentals of security. For instance… [a] forward-thinking policy is to designate a cross-functional team that coordinates and communicates security issues.”
The publicity surrounding cyber attacks and data security breaches has driven risk awareness. The good news is that the 2013 Information Security Breaches Survey conducted by PWC found that managing data breach risks is being prioritized by organizations and that has translated into budgets increasing, or at least not being cut. As a baseline, 84.15% of the companies we survey reported spending money on technology to address privacy-related matters. Probably most interesting in the data breach context is the amount of influence privacy professionals have on data loss prevention technology that discovers, monitors, and protects confidential data.
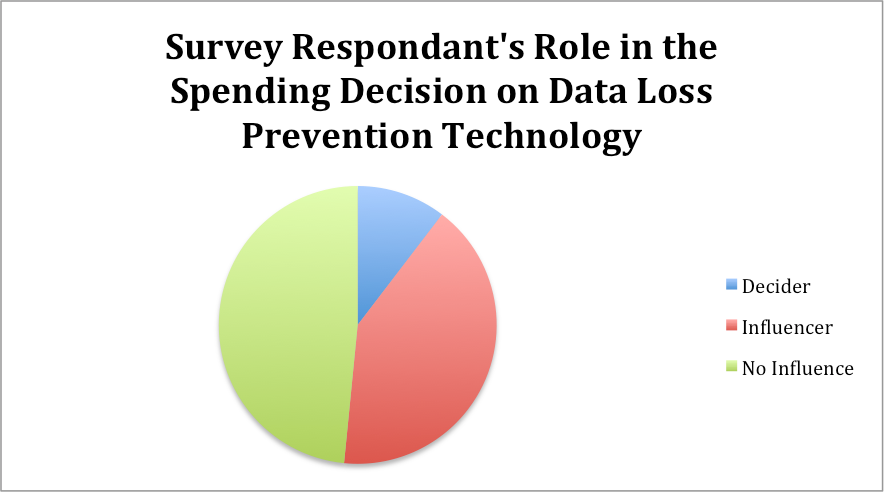
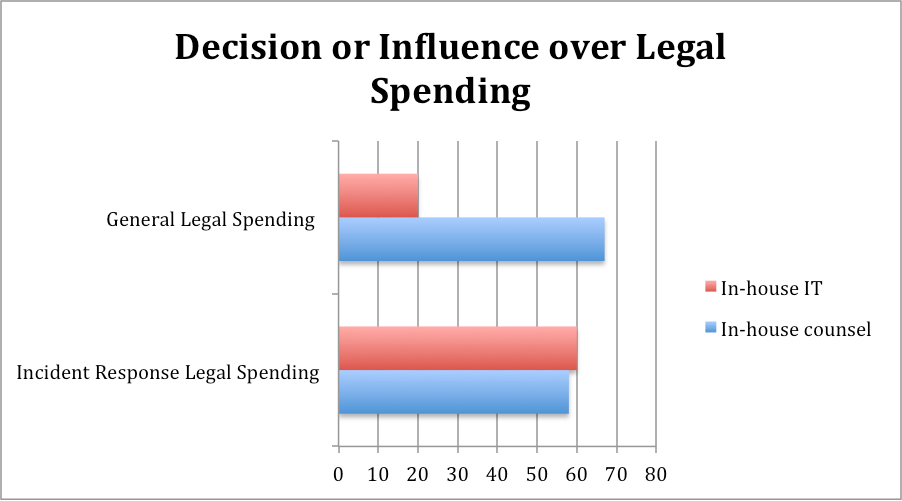
There are investigations and forensics, audit and consulting services, legal services, public relations and identity protection services that must be offered to affected consumers. Of course these are direct costs, the lost customer business (as just one data point, Target reported this month that its data breach contributed to a 5.3% reduction in sales, year over year) and higher customer acquisition cost that result have a large impact as well. While legal services are just one of many costs involved with recovering from a breach, they are a service that many privacy professional have some level of control over. Early analysis of the Industry of Privacy survey results has revealed some variation by position and industry in influence over legal spending on incident responses.
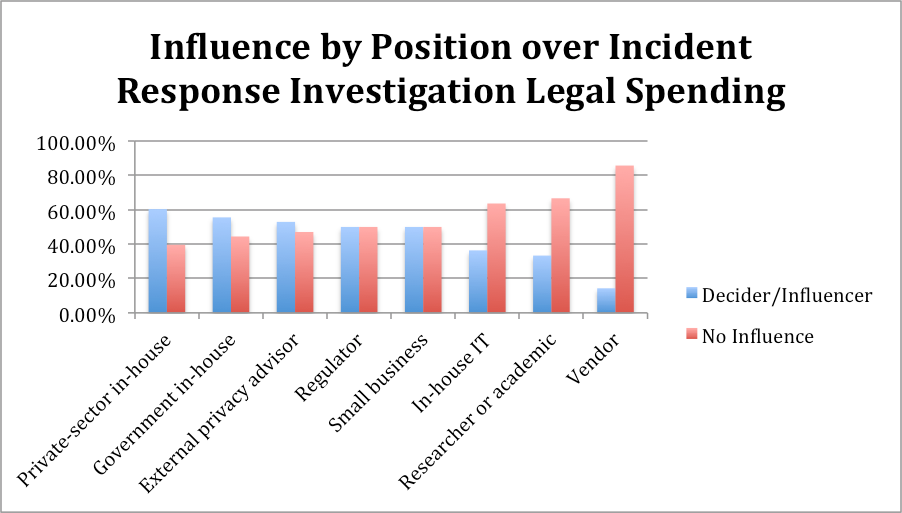
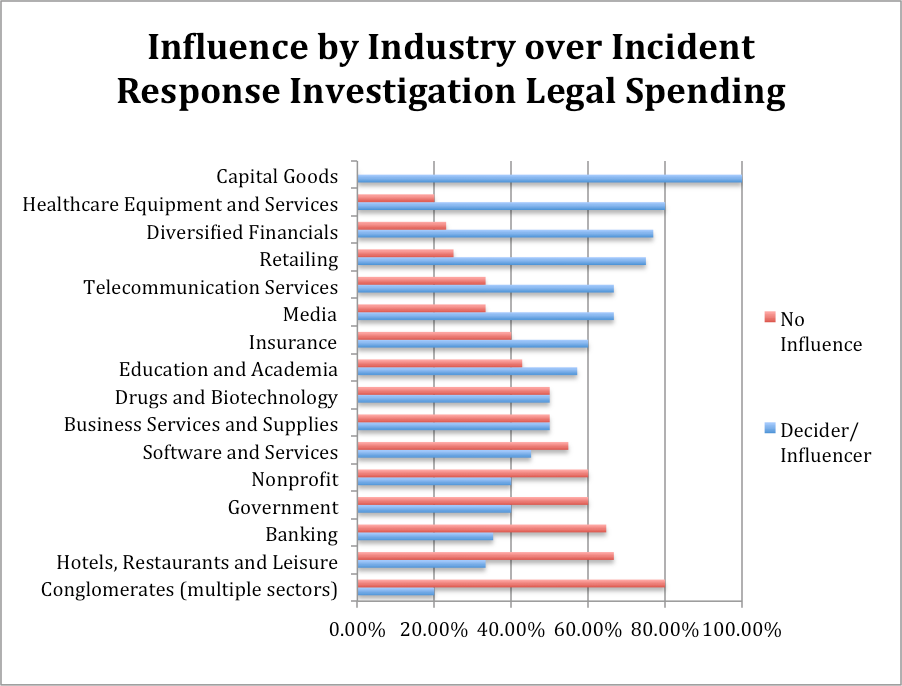
What is clear, however, is that in-house privacy professionals in the privacy sector play significant roles in both data breach prevention and data breach response, both operationally, as we might expect, and budgetarily.
Conclusion
The IAPP Industry of Privacy Study has only just begun but these early insights give you a taste of what’s to come. It’s clear that there are many opportunities in the privacy industry for technology vendors, service providers, law firms, consultants and other firms to develop products and services that offer solutions to the privacy concerns that abound in the marketplace. Our survey has disclosed a number of interesting trends. The percentage of companies that reported spending specifically on privacy-related technologies only varied, on average, 5 percent across all company size ranges. Small companies reported spending some portion of their budget on privacy enhancing technologies at nearly the same rate as large companies, and this demonstrates how far privacy has penetrated into every business’ budget. Professionals in large companies are more often in control of privacy spending but it’s not by the margins that were expected. The survey and interviews with industry experts revealed that many privacy positions are stakeholders rather than budget holders for privacy spending, but this still leaves them in a position to bring vendors and service providers to the table. The influence of privacy professionals over spending will be something the IAPP tracks over time and we’ll see whether that influence will increase, as many have predicted.
It's easy to focus on the complicated privacy rules, laws and regimes to define the field of privacy, but privacy is more than policy. It is a complicated economy with any number of buyers and sellers. The Industry of Privacy Project is still in its early days but capturing more information about what the industry has become, who participates in this industry, and how they carry out their work should allow professionals to benchmark themselves against their peers and ultimately help privacy pros to increase their value to their respective organizations.
The IAPP has created the first iteration of its Privacy Industry Index (PII). Check out Privacy Industry Index (PII): Data Breach Vendors in the IAPP Resource Center for links to vendors who provide consulting services, legal services, information technology, cyber liability insurance and help with consumer considerations.



